We help companies effectively manage access and permissions by adapting IAM (Identity and Access Management) solutions to their IT infrastructure. We specialize in integrating, updating, and optimizing authorization systems based on proven cybersecurity standards. This ensures organizations have full control over user identities, minimize the risk of unauthorized access, and effectively protect their data.nd upgrading authorization systems using renowned cybersecurity standards.
Keycloak services -
comprehensive implementation, maintenance, and training
Keycloak – what is it and how can we help you?
Keycloak is an open-source identity and access management platform that enables user authentication and permission management in applications and IT systems. It supports standards such as OAuth2, OpenID Connect, and SAML, allowing secure integration with various environments.
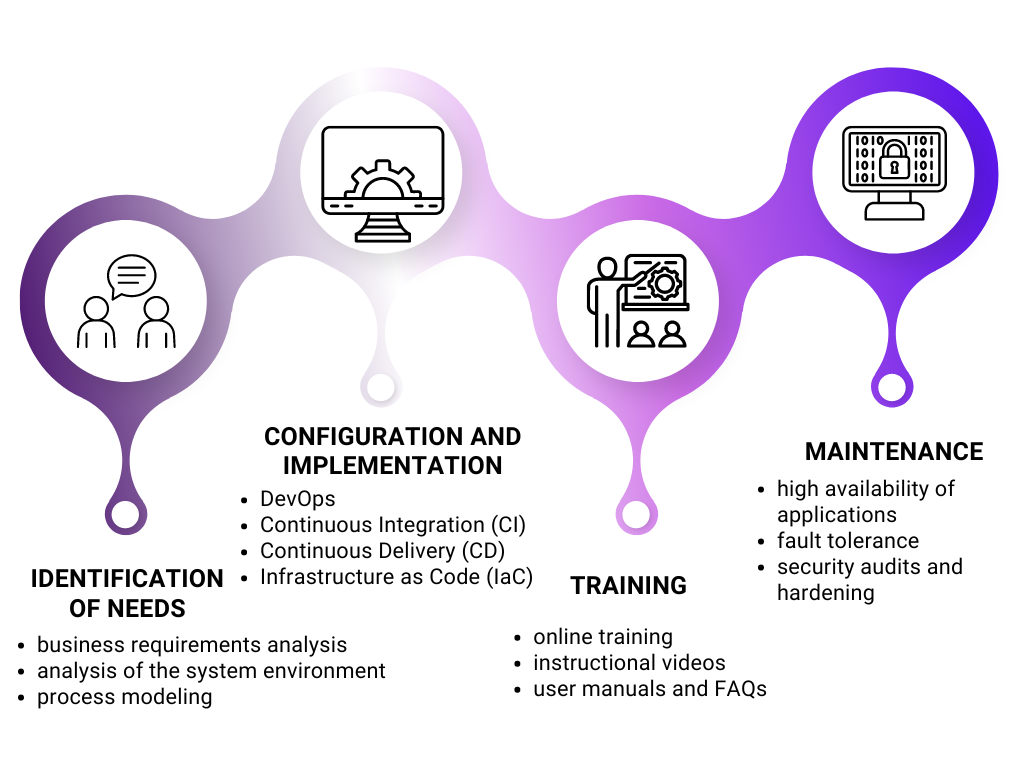
We provide support at every stage of Keycloak implementation – from installation and configuration to integration with your systems, optimization, and customization to meet specific business needs. We also assist with migration, updates, and offer training and security audits.
Main features supported by Keycloak
Keycloak provides a comprehensive identity and access management solution, enabling secure authentication, Single Sign-On (SSO), and user authorization for web and mobile applications. It supports industry-standard protocols such as OAuth 2.0, OpenID Connect, and SAML, allowing seamless integration with various authentication providers, including social logins and enterprise directories. With features like multi-factor authentication (MFA), role-based access control (RBAC), and centralized session management, Keycloak enhances security while simplifying identity management. Designed for flexibility, it can be deployed on-premises or in the cloud, making it a scalable choice for organizations of all sizes.
Single Sign-On
(SSO)
allows a user to access multiple applications after logging in just once, using credentials such as username and password, as well as other methods. In the Keycloak system, this process is supported by the OpenID Connect (OIDC) protocol, which manages the exchange of identity information and user authentication data.
Integration with Identity Management Systems (IdM)
Keycloak can be integrated with other IdM systems, such as LDAP (Lightweight Directory Access Protocol) or Active Directory, allowing for centralized management of user identities and permissions within an enterprise. Such integration enhances SSO capabilities and includes user federations, enabling even more consistent and efficient management of access to various systems and applications.
Multi-Factor Authentication (MFA)
This feature provides an additional layer of security by using multiple methods of user identity verification at the same time, which significantly hinders unauthorized access. 2FA (Two-Factor Authentication) is a popular form of MFA, often requiring the user to enter a password and confirm their identity with a second factor, such as a code from an authentication app.
Identity Providers (IdPs)
It enables user authentication using various configured sources that support standard protocols such as OAuth2 and OpenID Connect. As a result, the Keycloak system is extremely flexible and can integrate with various identity management services, including Google and Facebook.
Single Logout
Logging out from one system as part of SSO automatically logs the user out of all associated systems. This makes user session management more efficient and secure.
Session Management
Keycloak controls user session activity at the server level, allowing for monitoring and management of session lifetimes and their secure termination.
“Effective identity management is a challenge, but with the right approach, it can become a key asset for your organization. At Inero Software, we specialize in implementing, configuring, and managing IAM systems based on Keycloak. With our expertise, we help companies avoid common pitfalls, successfully deploy SSO and MFA, and tailor Keycloak to their specific needs.
Do you want to implement Keycloak efficiently and ensure a secure, scalable identity management system for your organization? Contact us—we’ll help you plan the infrastructure, choose the best configuration, and avoid costly mistakes.”
Andrzej Chybicki, PhD eng.
CEO, Inero Software

Our team will implement Keycloak for you
Inero Software provides comprehensive Keycloak services, enhancing cloud security across platforms such as AWS and Azure AD Active Directory. Our experts deploy Keycloak solutions within Docker containers, ensuring efficient management and scalable deployments. We specialize in advanced solutions for access and permission management, compliant with the OAuth2 protocol for secure authentication across various platforms. Whether integrating with existing Identity Management Systems or configuring new Identity Providers, our team ensures a seamless setup and ongoing support.
We have many years of experience and a rich portfolio of completed projects for corporate clients in access and permission management. We create advanced solutions for managing users and their roles, tailored to various IT infrastructures. Our team consists of experienced programmers, allowing us to implement complex authorization schemes using renowned standards and tools, in accordance with corporate security policies. Our solutions are based on the Open Authorization protocol.
Advantages of Keycloak
The ability to define and manage attributes that are assigned to a user account, such as roles, access rights, preferences, or customization settings.
The ability to track and report user activities and their compliance with internal security policies and external legal regulations.
(MFA) Security method requiring identity confirmation through two or more independent components, such as password, token, or biometric methods like Windows Hello.
group management
Centralized access control, flexibility in user management, and streamlined login processes through Single Sign-On (SSO).
Automatic scaling of Keycloak in Kubernetes ensures high availability and flexibility by adjusting resources according to current loads.
The ability to customize themes to tailor Keycloak interfaces, achieving visual consistency with the entire corporate infrastructure.
They recommend us

“The previous experience of our cooperation allows us to recommend Inero Software sp. z o.o. as a reliable and professional technological partner in the field of developing dedicated software for internet solutions, cybersecurity, and mobile applications.
The collaboration with the partner was smooth, timely, and maintained appropriate standards. The company demonstrated a high level of commitment to the project and, thanks to a professional approach, we were able to jointly achieve the set business goals for the logistics solutions area implemented for Sygnity S.A. clients.”
Leszek Adam Frączek
Visit our blog

FAQ
| Question | Answer |
|---|---|
| What are the main advantages of Keycloak? | Keycloak implements industry-standard protocols such as OAuth and OpenID Connect, and its developers regularly update the solution in line with the latest security guidelines and best practices. This ensures up-to-date and secure authentication mechanisms without requiring application developers to be involved. |
| Why migrate to Keycloak? | Migrating to Keycloak is beneficial due to its automatic updates that comply with industry security standards, as well as the ability to delegate identity and authorization management to a specialized tool, reducing the burden on application developers. |
| What technologies does Keycloak support? | Keycloak supports OAuth, OpenID Connect, and SAML protocols. It is designed to be technology-independent, meaning it can be integrated with virtually any application using REST conventions. |
| Who develops Keycloak? | Keycloak is an open-source project created by enthusiasts and experts from around the world. The primary contributors to the Keycloak code repository are developers from RedHat. Since 2024, Keycloak has also been a member of the Cloud Native Computing Foundation (CNCF), which was founded by the Linux Foundation to develop open, community-supported standards and software. |
| How much does Keycloak cost? | Keycloak is available under the Apache 2.0 license—its use does not involve any licensing fees. The Keycloak license has no time limitations and does not restrict the number of instances, users, integrated applications, or other usage aspects. |
| Is Keycloak secure? | Yes, Keycloak implements industry-standard security protocols, and its developers ensure that the software is always compliant with the latest security guidelines. |
| Can I manage users in Keycloak by myself? | Yes, Keycloak provides a graphical management interface accessible via a web browser. It allows administrators to manage users, applications integrated with Keycloak, and permissions in the form of roles and user groups. |
| How can I migrate users to Keycloak from other databases? | Keycloak provides APIs that allow importing user data from previous databases or identity servers. |
| Can I configure social media login in Keycloak? | Yes, Keycloak supports login through popular social media platforms such as Google, Facebook, LinkedIn, and GitHub, and allows integration with other identity providers via the OpenID Connect protocol. |
| How difficult is it to deploy Keycloak? | The complexity of deploying Keycloak depends on the number of applications to be integrated, the protocols they support, and existing directory services. For smaller environments, deployment can be straightforward, but in large enterprises with complex infrastructure, advanced configuration may be required. |
| Does Keycloak support Single Sign-On (SSO)? | Yes, Keycloak enables Single Sign-On (SSO), allowing users to log in once and access multiple applications simultaneously with the appropriate permissions. |
| Can Keycloak help prevent phishing attacks against my organization? | Keycloak offers tools and mechanisms to minimize the risk of phishing attacks. It allows customization of email templates for registration and password reset, as well as login pages (themes) in the SSO process, helping users recognize legitimate communications. Additionally, Keycloak supports multi-factor authentication (MFA), providing an extra layer of security aligned with the latest security standards. |

